Enterprise Tester and Okta
Enterprise Tester is a SAML 2.0 enabled application within OKTA.
Okta is an enterprise-grade, identity management service, built for the cloud, but compatible with many on-premises applications. With Okta, IT can manage any employee's access to any application or device. Okta runs in the cloud, on a secure, reliable, extensively audited platform, which integrates deeply with on-premises applications, directories, and identity management systems.
Configuring Okta
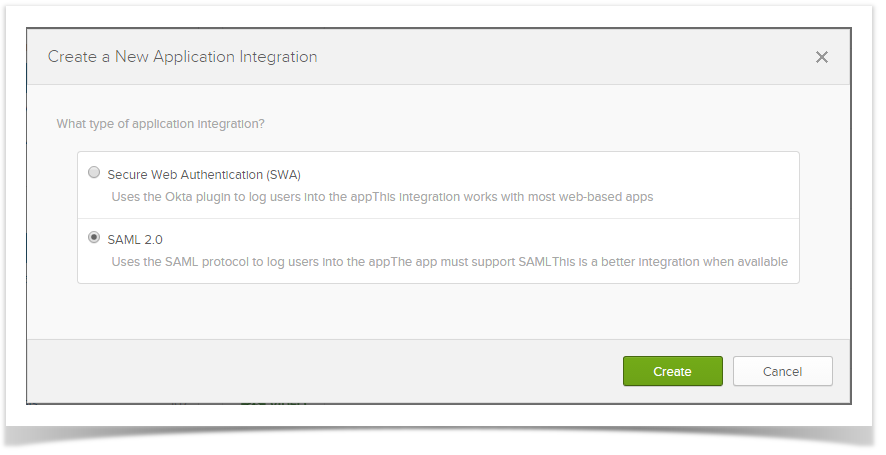
1) In Okta, create Enterprise Tester integration using SAML 2.0.
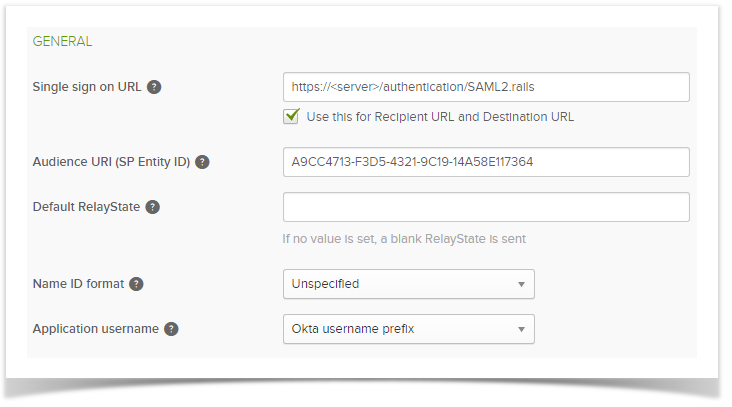
2) In Okta the SAML General Settings need to contain the following.
- Single Sign URL - this must be your Enterprise Tester instance e.g https://enterprisetester/authentication/SAML2.rails
- Audience URI - this is A9CC4713-F3D5-4321-9C19-14A58E117364
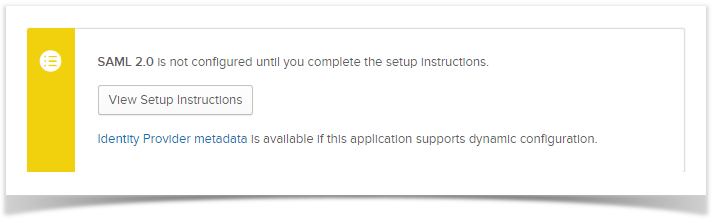
3) Make sure you record IDP information when selecting the "View Setup Instructions".
Configuring Enterprise Tester to use Okta
Add the following keys to the appSettings section in the Enterprise Tester web.config file. Note: Values used within these appsettings will be available after completing the Okta configuration above.
1) Enable SAML Support
<add key="SAML.Enabled" value="true" /> |
|
3) IDP Issuer
<add key="SAML.Issuer"value="<IDP Issuer>"/> |
4) IDP SSO URL
<add key="SAML.IDP"value="<IDP SSO URL>"/> |
5) X.509 Certificate
<add key="SAML.Certificate"value="<X.509 Certificate>"/> |
6) Specify logout url
Do not add an Enterprise Tester URL here or users will be automatically logged back into Enterprise Tester.
<add key="SAML.Logout"value="https://your_selected_logout_page"/> |
SHA-256 XML Signature Support
SAML 2.0 uses the SHA-256 encryption protocol if this is not enabled on your server you will need to enable it.